SAP GRC ARA Configuration Step-by-Step Guide (Real-Time)
Want hands-on SAP training? 👉 SAP Security GRC Training in Hyderabad
What is ARA in SAP GRC?
ARA (Access Risk Analysis) helps identify access risks, detect SoD conflicts, and maintain compliance in SAP systems.
- Detect conflicting roles
- Identify risky access
- Ensure secure authorization
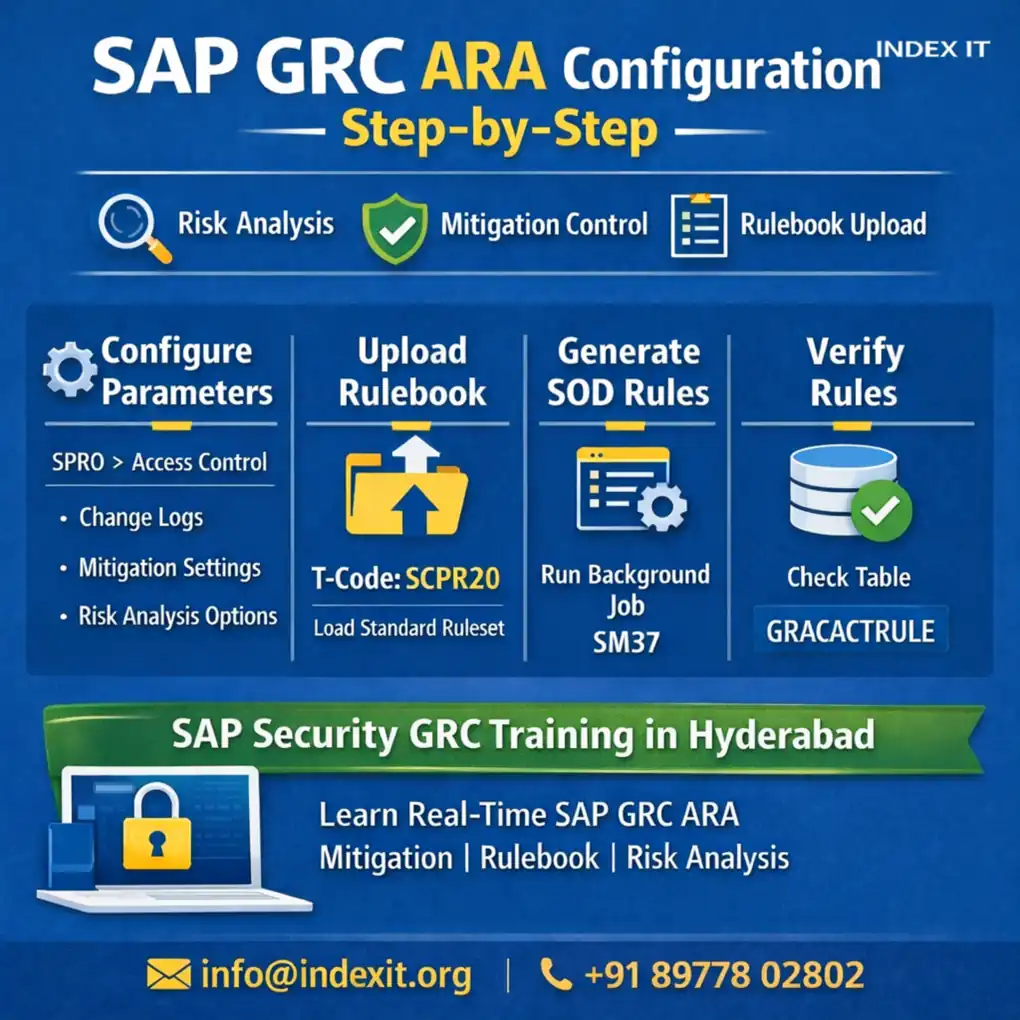
Step 1: ARA Configuration
Path: SPRO → Governance, Risk & Compliance → Access Control → Maintain Configuration Settings
Types of Parameters
1. Change Log
Tracks changes in functions, risks, roles, and rule sets.
2. Mitigation (Important)
Mitigation allows risky access with control.
Example: User needs SU01 and PFCG → system shows risk → apply mitigation → access allowed with monitoring.
3. Risk Analysis Parameters
- Include locked users
- Include expired users
- Default SOD report
4. Workflow Parameters
Used for approvals, access requests, and mitigation workflows.
Step 2: Rulebook (SOD Rules)
Rulebook contains business processes, functions, risks, and rule sets.
Without rulebook → No risk analysis
Step 3: Upload Rulebook
Use T-code: SCPR20
- Select BC Set
- Activate rulebook
Step 4: Generate Rules
Path: SPRO → Generate SOD Rules
Check job using SM37
Step 5: Verify Rules
Check table: GRACACTRULE
Step 6: Run Risk Analysis
- Select user
- Select connector
- Execute analysis
Real-Time Implementation Flow
- Post installation
- Configuration
- Parameter setup
- Rulebook upload
- Rule generation
- Risk analysis
Master SAP GRC with real-time training 👉 SAP Security GRC Course in Hyderabad
SAP GRC Training in Hyderabad
If you are searching for:
- SAP GRC training in Hyderabad
- SAP Security course
- ARA real-time training
Index IT provides hands-on training, real-time scenarios, and placement support.
Start your SAP career today 👉 Join SAP Security GRC Training